Table of Contents
Cloud networking has fundamentally transformed the way businesses design, deploy, and manage their IT infrastructure.
As organisations increasingly migrate workloads to the cloud, understanding how cloud networks operate has become a core competency for IT leaders, architects, and developers alike.
In early cloud models, all resources resided in a shared, multi-tenant environment, offering scalability but little control over network boundaries.
As cloud adoption matured, the demand for isolated, secure environments grew significantly.
Businesses running sensitive workloads, from financial transactions to patient health records, needed more than shared infrastructure could offer.
Virtual Private Cloud (VPC) sits at the heart of modern cloud infrastructure.
It acts as the foundational networking layer on which virtually all cloud-hosted services are built, from web applications and databases to AI workloads and hybrid cloud extensions.
Without a well-designed VPC, even the most robust applications can be exposed to unnecessary security risks.
What is a Virtual Private Cloud (VPC)?
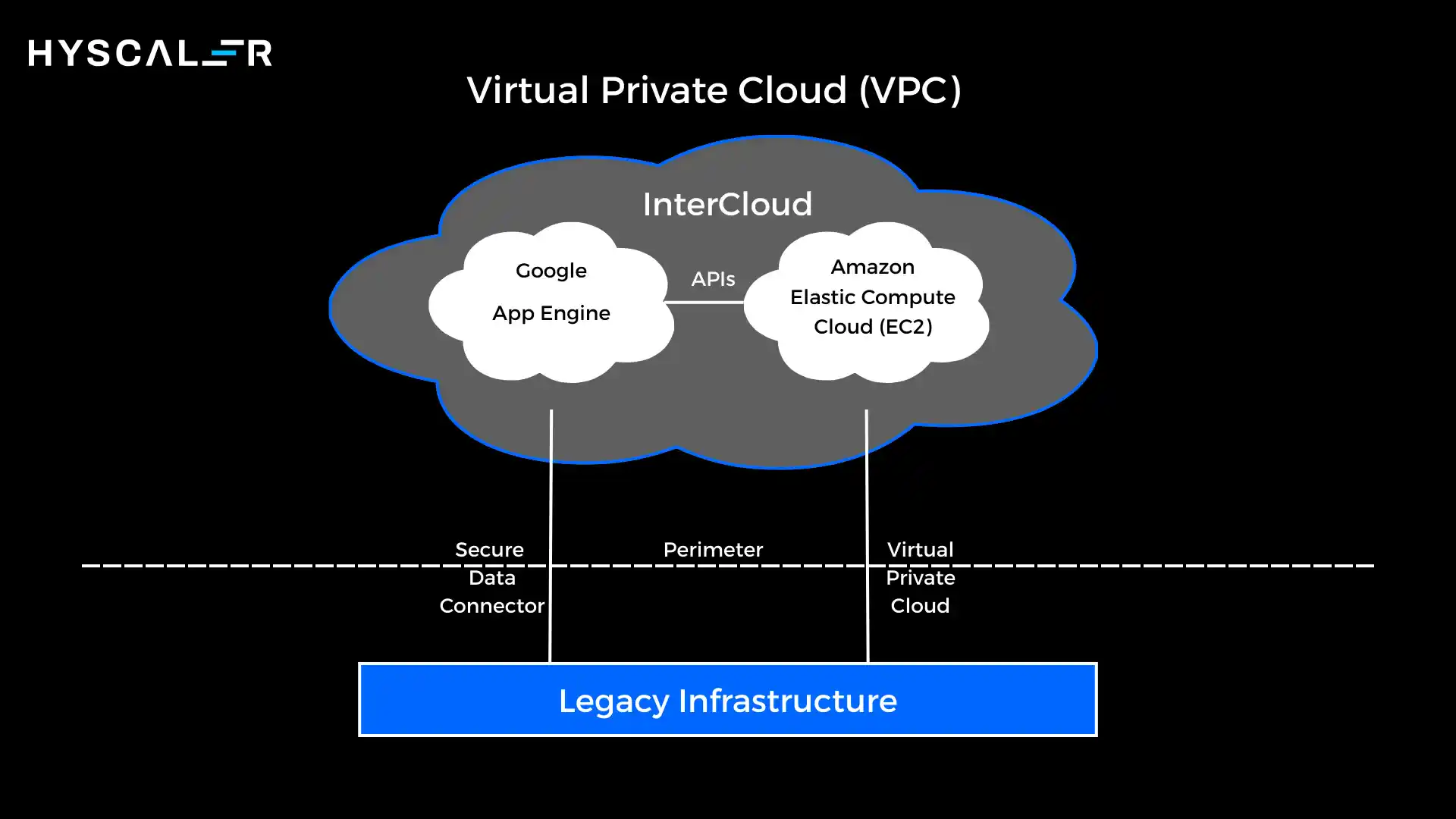
A Virtual Private Cloud is a private, isolated network environment that exists within a public cloud platform, such as AWS, Microsoft Azure, or Google Cloud.
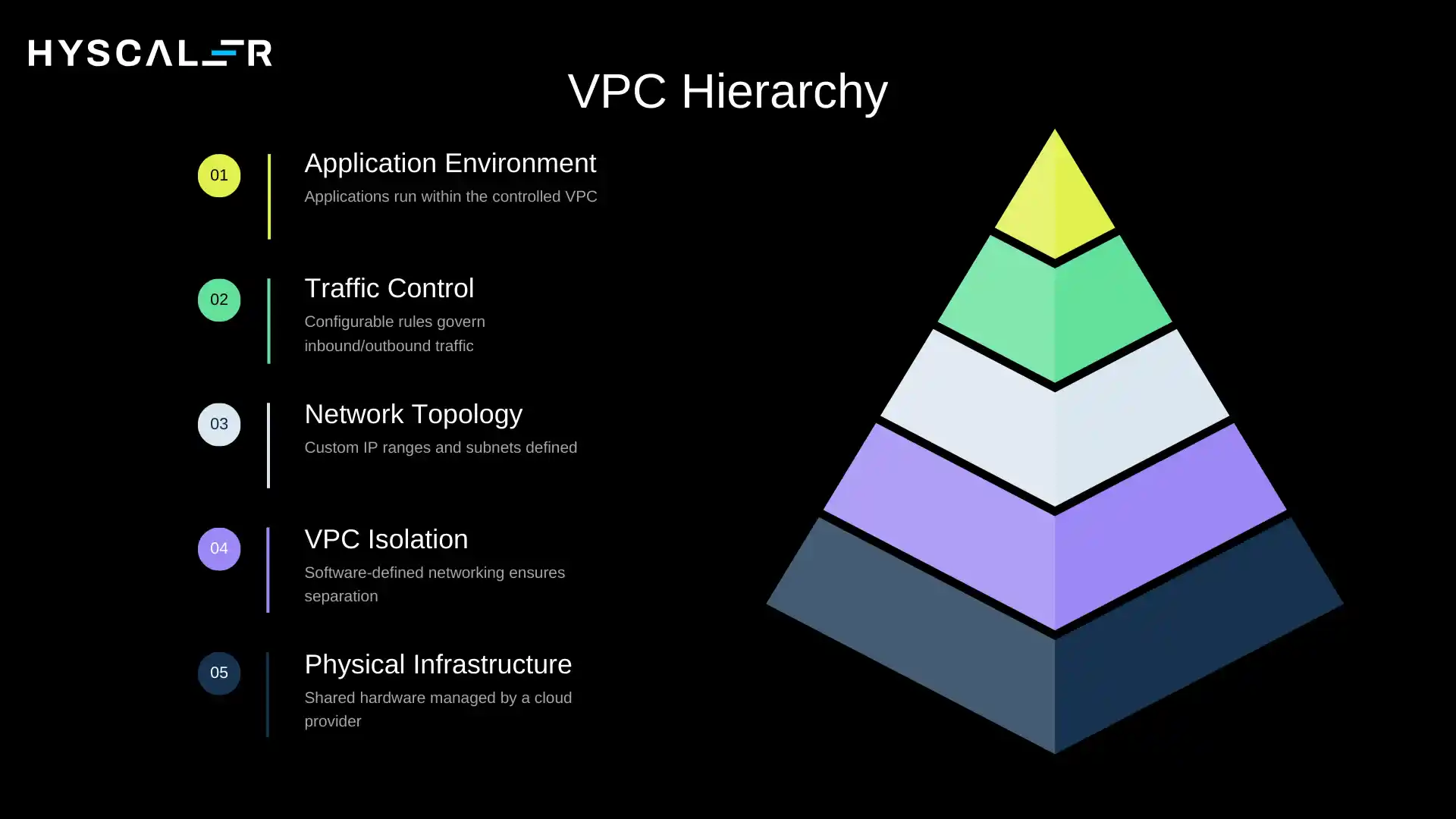
Despite running on shared physical infrastructure, a VPC behaves as though it were a dedicated private network, with its own IP address space, subnets, routing rules, and security policies.
In practice, a VPC allows you to define a custom network topology, selecting your own IP ranges, dividing your network into subnets, and controlling all inbound and outbound traffic through configurable rules.
The public cloud provider handles the physical infrastructure, but your VPC exists as a logically separate environment that other tenants on the same hardware cannot access.
How Virtual Private Cloud Works in Public Cloud Environments
When you create a Virtual Private Cloud, you are essentially carving out a segment of the cloud provider’s network fabric and claiming it as your own.
The cloud platform enforces isolation using software-defined networking (SDN), ensuring that packets from other tenants never reach your resources unless explicitly allowed.
Within your VPC, you can create multiple subnets, both public-facing and internal, and configure route tables, gateways, and security rules that govern how traffic moves in and out.
Your applications run inside this controlled environment, communicating with each other and the outside world strictly according to rules you define.
Real-World Example of a VPC Deployment
Consider an e-commerce company running on AWS.
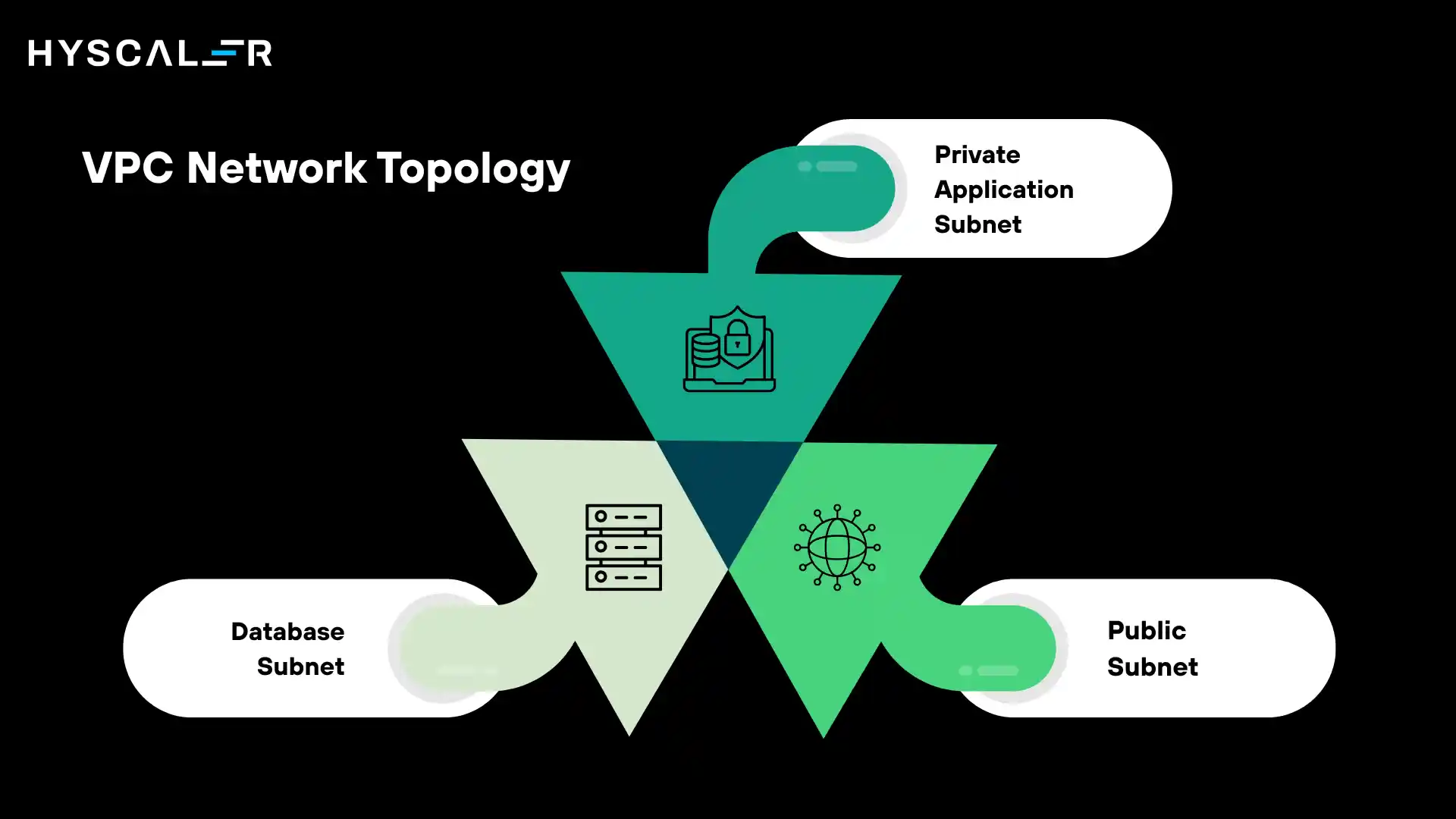
Their architecture might include a VPC with three layers:
A public subnet hosting a load balancer and web servers that accept traffic from the internet.
A private application subnet running business logic.
And a database subnet with no internet access whatsoever.
Traffic flows from the internet into the public subnet, gets processed by the application tier, and data is read or written in the isolated database layer, all within a single, tightly controlled VPC.
Why VPC is Important for Modern Cloud Architecture
As cloud infrastructure becomes the backbone of enterprise operations, the stakes for network security have never been higher.
VPCs address several critical requirements that businesses must meet in today’s environment.
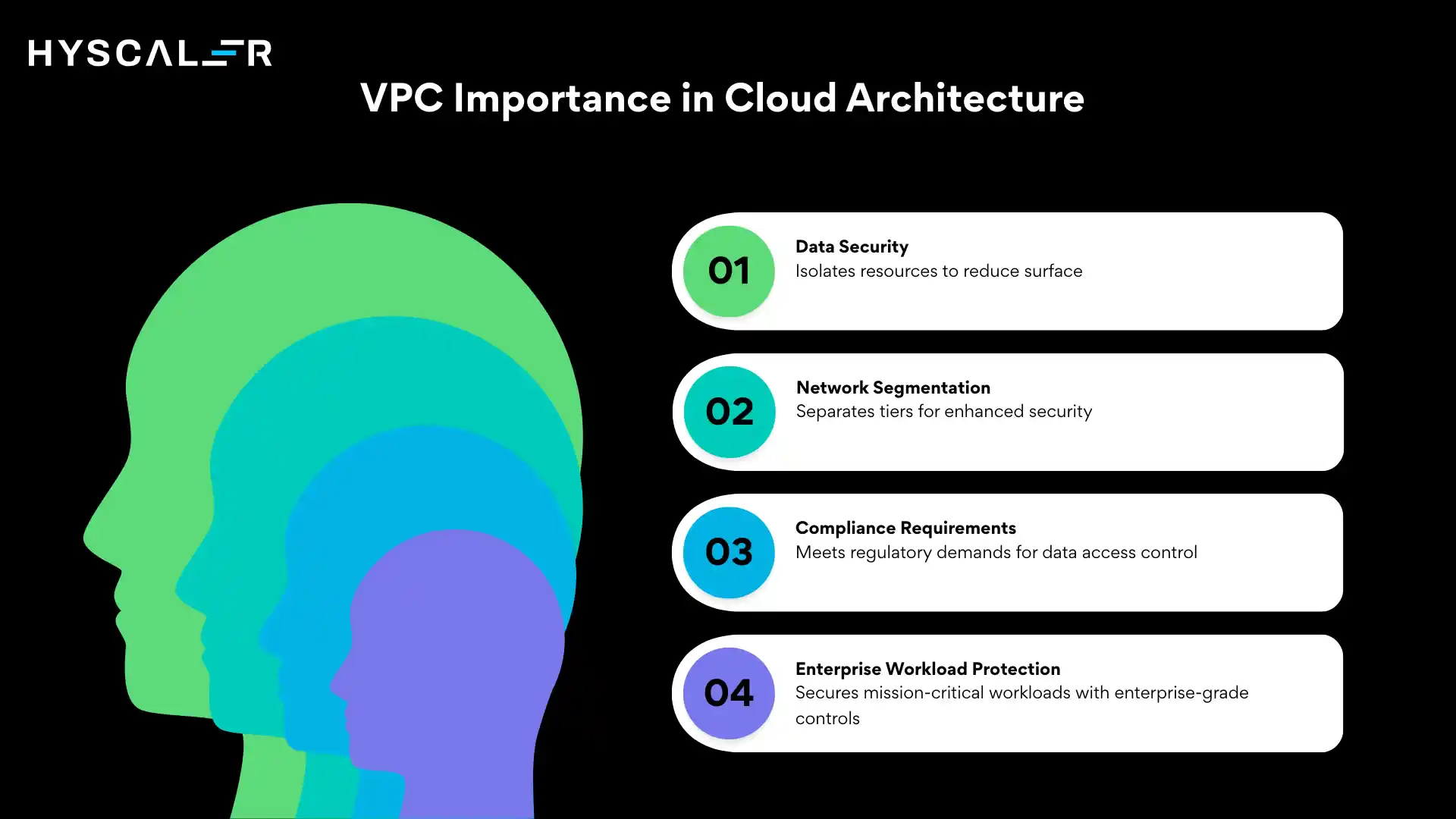
Data Security and Privacy
By isolating your cloud resources in a private network, a Virtual Private Cloud dramatically reduces your attack surface.
Resources in private subnets are not reachable from the public internet, meaning potential attackers have far fewer entry points.
Even within the VPC, traffic between components can be restricted using security groups and network ACLs.
Network Segmentation
Modern applications typically comprise multiple tiers: web, application, and data.
VPCs allow each tier to be placed in its own subnet with specific access controls, ensuring that a compromise in one layer does not automatically expose the others.
Compliance Requirements
Many regulatory frameworks, including HIPAA, PCI-DSS, GDPR, and SOC 2, require organisations to demonstrate strict controls over data access and network boundaries.
A properly configured Virtual Private Cloud provides the documented, auditable network isolation these frameworks demand.
Enterprise Workload Protection
Large enterprises running mission-critical workloads, such as ERP systems, trading platforms, or proprietary data pipelines, need guarantees that their cloud environments are as secure as their on-premise data centres.
VPCs deliver that assurance with enterprise-grade controls built natively into the cloud.
Key Components of a Virtual Private Cloud
A Virtual Private Cloud is composed of several interconnected components that together define how your private cloud network is structured and how traffic flows through it.
Understanding each component is essential to designing a secure and efficient cloud architecture.
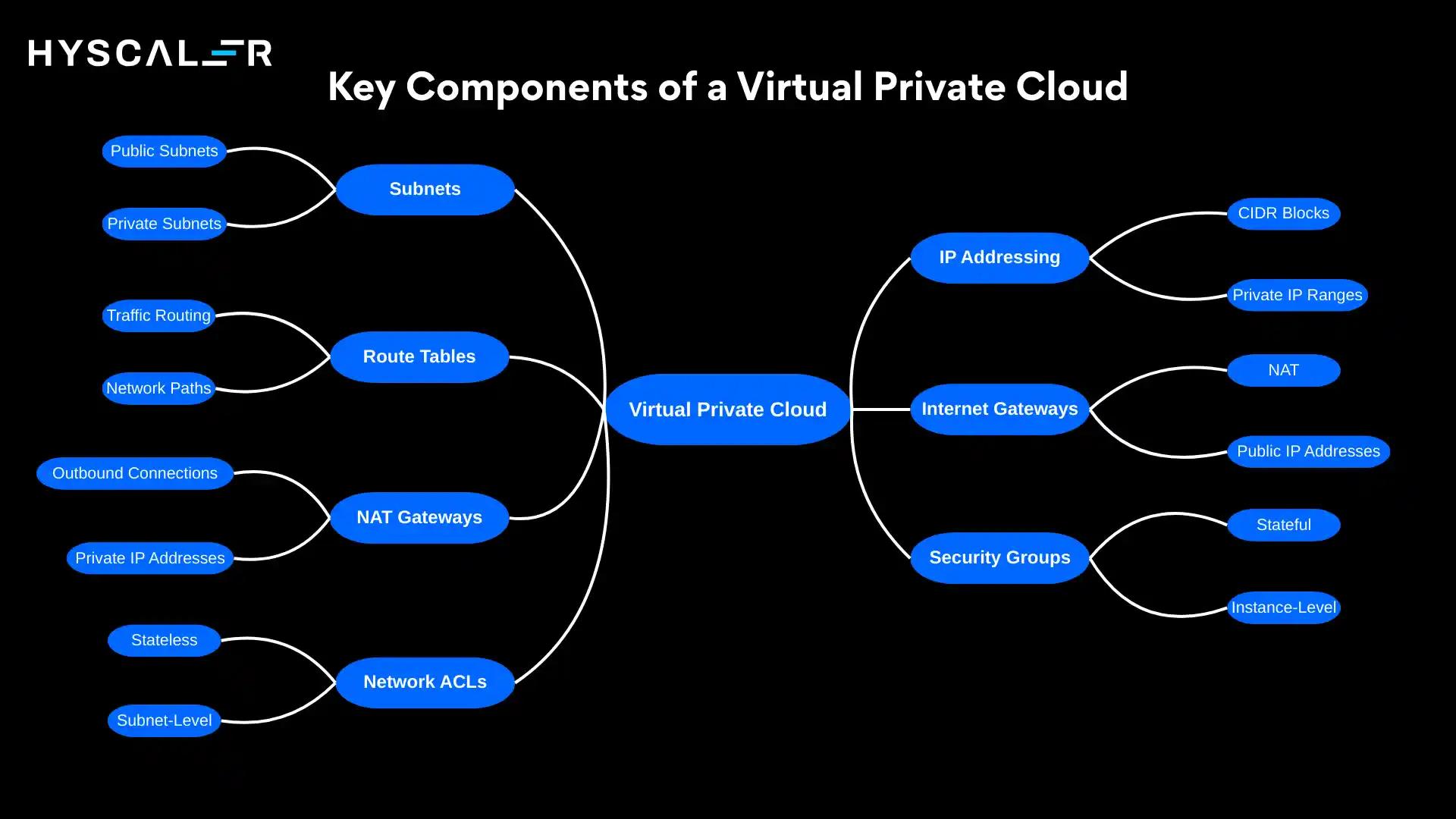
Subnets
Subnets are subdivisions of your VPC’s IP address space.
They allow you to logically partition your network for different purposes and apply different levels of access control to each partition.
Public Subnets
A public subnet has a route to an Internet Gateway, meaning resources within it, such as web servers and load balancers, can be reached directly from the internet.
Public subnets are designed for resources that must serve external users.
Private Subnets
Private subnets have no direct route to the internet.
Resources here, such as application servers, databases, and internal services, are accessible only from within the VPC or through explicitly allowed connections.
This makes private subnets the preferred home for sensitive workloads.
IP Addressing
CIDR Blocks
When you create a Virtual Private Cloud, you assign it a CIDR (Classless Inter-Domain Routing) block, a range of IP addresses.
For example, 10.0.0.0/16 gives you 65,536 addresses. Each subnet within the VPC gets a portion of this range.
Private IP Ranges
Resources within a VPC are assigned private IP addresses from ranges defined in RFC 1918 (e.g., 10.0.0.0/8, 172.16.0.0/12, 192.168.0.0/16).
These addresses are not routable on the public internet, adding another layer of isolation.
Route Tables
Traffic Routing
Route tables contain rules that determine where network traffic is directed.
Each subnet is associated with a route table, and each rule specifies a destination address range and a target, such as an Internet Gateway, a NAT Gateway, or another subnet.
Network Paths
By carefully configuring route tables, you control exactly which traffic paths exist within your VPC and which resources can communicate with each other.
A private subnet’s route table, for instance, might route internal traffic freely while blocking any route to the internet.
Internet Gateways
An Internet Gateway (IGW) is a horizontally scaled, redundant Virtual Private Cloud component that enables communication between your VPC and the public internet.
It performs Network Address Translation (NAT) for resources with public IP addresses, allowing them to send and receive traffic to and from the internet.
Only public subnets with a route pointing to the IGW can access the internet directly.
NAT Gateways
A NAT (Network Address Translation) Gateway allows resources in a private subnet to initiate outbound connections to the internet, for example, to download software updates, without being directly accessible from the internet.
The NAT Gateway sits in a public subnet and translates the private IP addresses of outbound requests to its own public IP, keeping your private resources fully shielded from unsolicited inbound traffic.
Security Groups
Security groups are stateful, instance-level virtual firewalls.
They control which inbound and outbound traffic is allowed for individual resources, such as virtual machines or containers.
A security group rule specifies a protocol, port range, and source/destination. Because they are stateful, a response to an allowed inbound request is automatically permitted outbound, and vice versa.
Network ACLs
Network Access Control Lists (NACLs) operate at the subnet level as a stateless firewall.
Unlike security groups, NACLs evaluate each packet independently; responses to allowed inbound traffic must be explicitly permitted in the outbound rules.
NACLs provide a coarser, additional layer of control and are typically used alongside security groups for defence-in-depth.
How Virtual Private Cloud Works
Understanding the flow of creating and configuring a Virtual Private Cloud helps demystify cloud networking.
Here is the typical architecture flow from initial setup to deploying a production application:
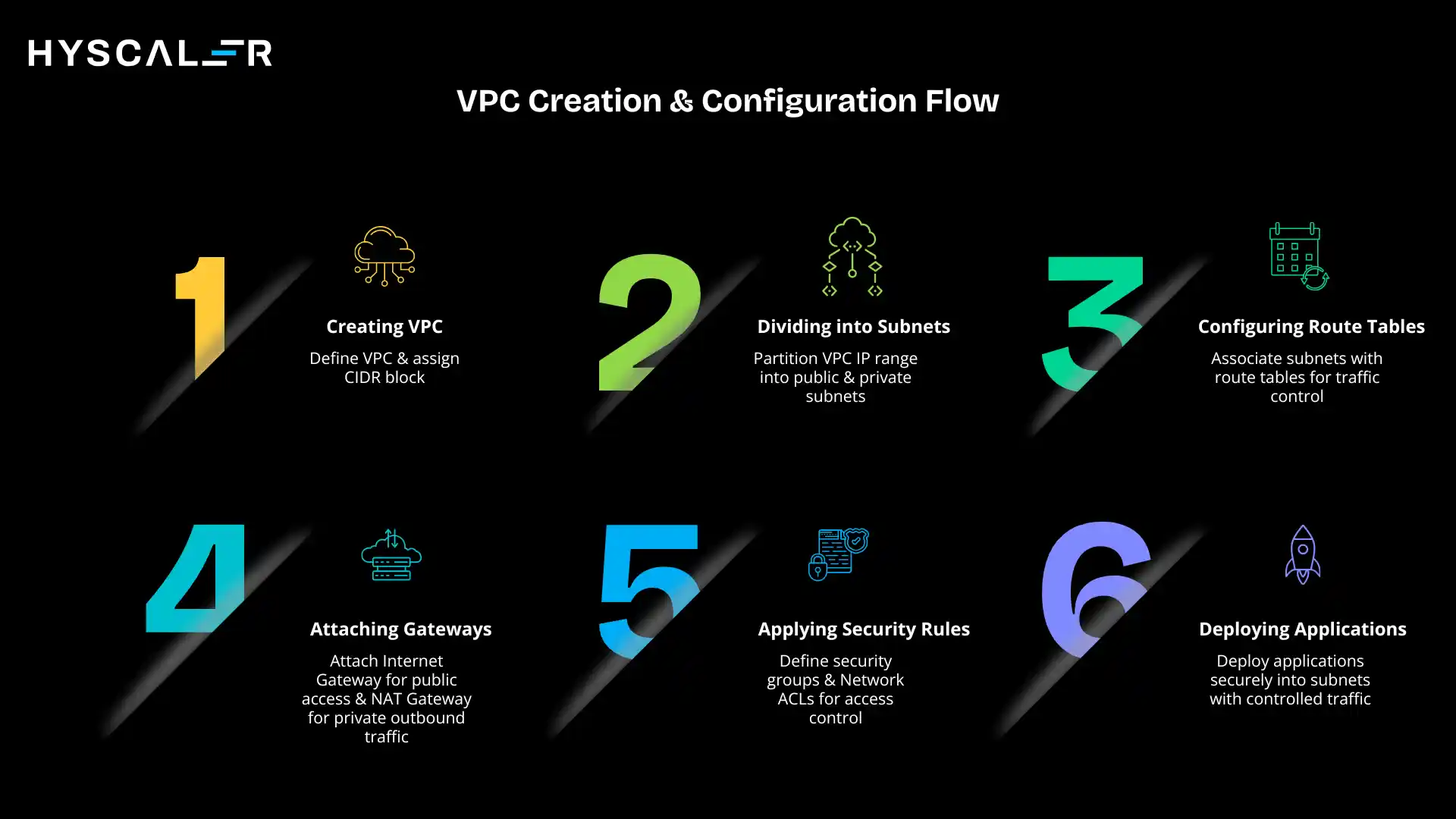
- Creating a VPC with IP Range – You begin by defining your VPC and assigning a CIDR block (e.g., 10.0.0.0/16) that determines the total pool of IP addresses available to all resources in the VPC.
- Dividing into Subnets – You partition the VPC’s IP range into subnets across one or more availability zones. Public subnets hold internet-facing resources; private subnets isolate backend services.
- Configuring Route Tables – Each subnet is associated with a route table. Public subnets get a route pointing to the Internet Gateway; private subnets route outbound traffic through the NAT Gateway.
- Attaching Internet or NAT Gateways – An Internet Gateway is created and attached to the VPC for public subnet internet access. NAT Gateways are deployed in public subnets to handle outbound traffic from private subnets.
- Applying Security Rules – Security groups are defined and assigned to individual resources. Network ACLs are configured at the subnet level for additional access control.
- Deploying Applications Securely – Applications, databases, and services are deployed into the appropriate subnets with all traffic controlled through the configured gateways, route tables, and security policies.
Key Benefits of Virtual Private Cloud
VPCs offer a wide range of strategic and operational advantages, making them the standard networking model for cloud-hosted enterprise infrastructure.
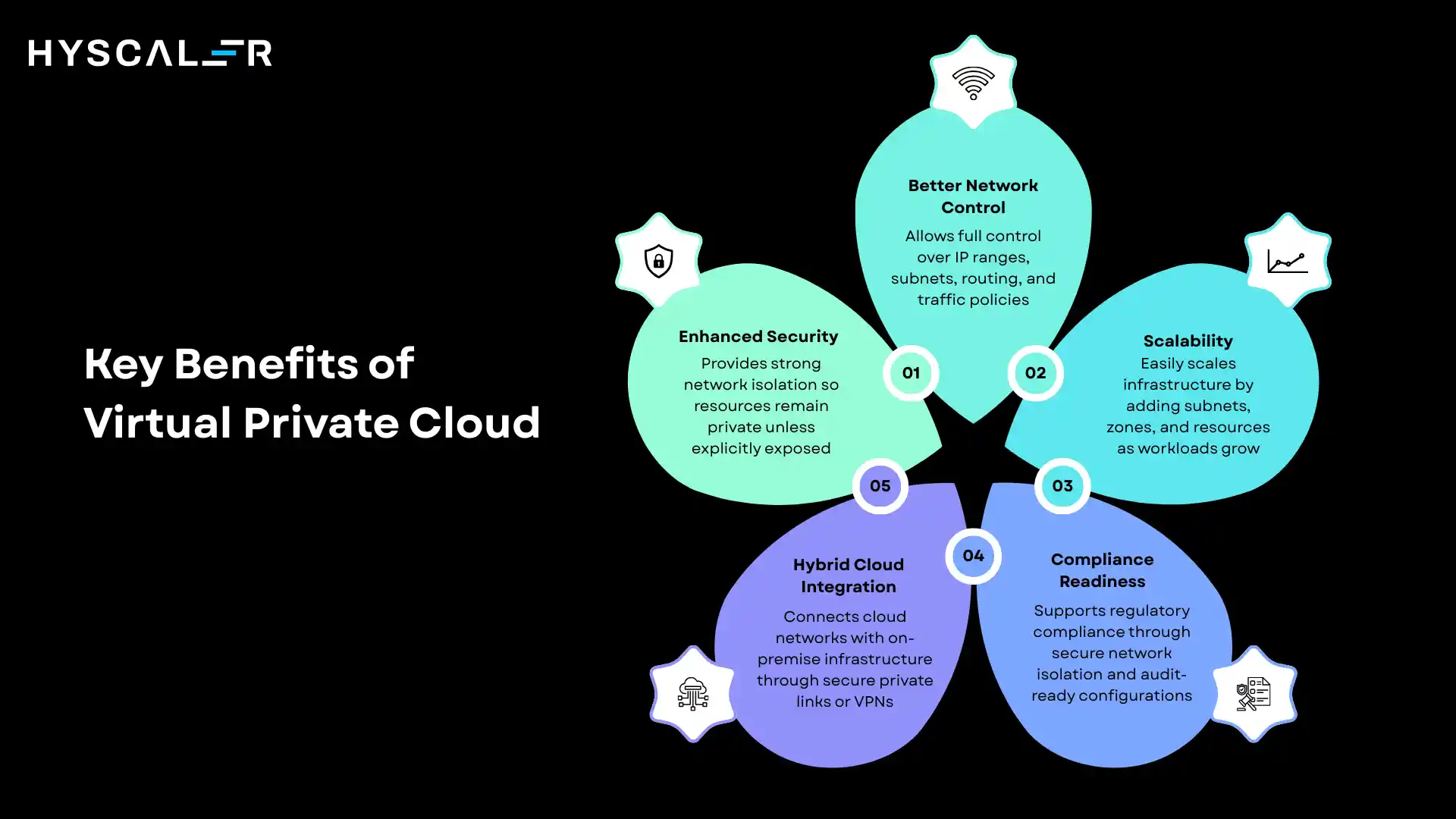
Enhanced Security
The most fundamental benefit of a Virtual Private Cloud is network isolation.
Resources within a VPC are not reachable from the public internet unless explicitly exposed, providing a strong default security posture.
Combined with security groups and NACLs, a VPC gives you granular, layered control over every network interaction within your environment.
Better Network Control
With a VPC, you own your network design.
You choose your IP address ranges, define subnet topologies, control routing, and decide exactly which traffic is allowed where.
This level of control, previously available only in on-premise data centres, is now available natively within the cloud.
Scalability
As your application grows, a VPC scales with it.
You can add new subnets, attach additional availability zones, deploy new compute resources, or expand your IP address range, all without redesigning your core network architecture.
Cloud-native elasticity is preserved within the secure boundary of your VPC.
Compliance Readiness
VPCs are a fundamental enabler of cloud compliance.
By providing network-level isolation, audit-ready configuration, and integration with logging and monitoring tools, VPCs help organisations demonstrate the controls required by HIPAA, PCI-DSS, GDPR, ISO 27001, and SOC 2, among others.
Hybrid Cloud Integration
VPCs integrate seamlessly with on-premise infrastructure.
Using VPN connections or dedicated private links (such as AWS Direct Connect, Azure ExpressRoute, or Google Cloud Interconnect), organisations can extend their private data centre networks directly into the VPC, enabling hybrid cloud architectures that treat cloud and on-premise resources as a unified, secure network.
Virtual Private Cloud (VPC) Architecture Example
A classic three-tier Virtual Private Cloud architecture illustrates how the components work together to create a secure, layered application environment:
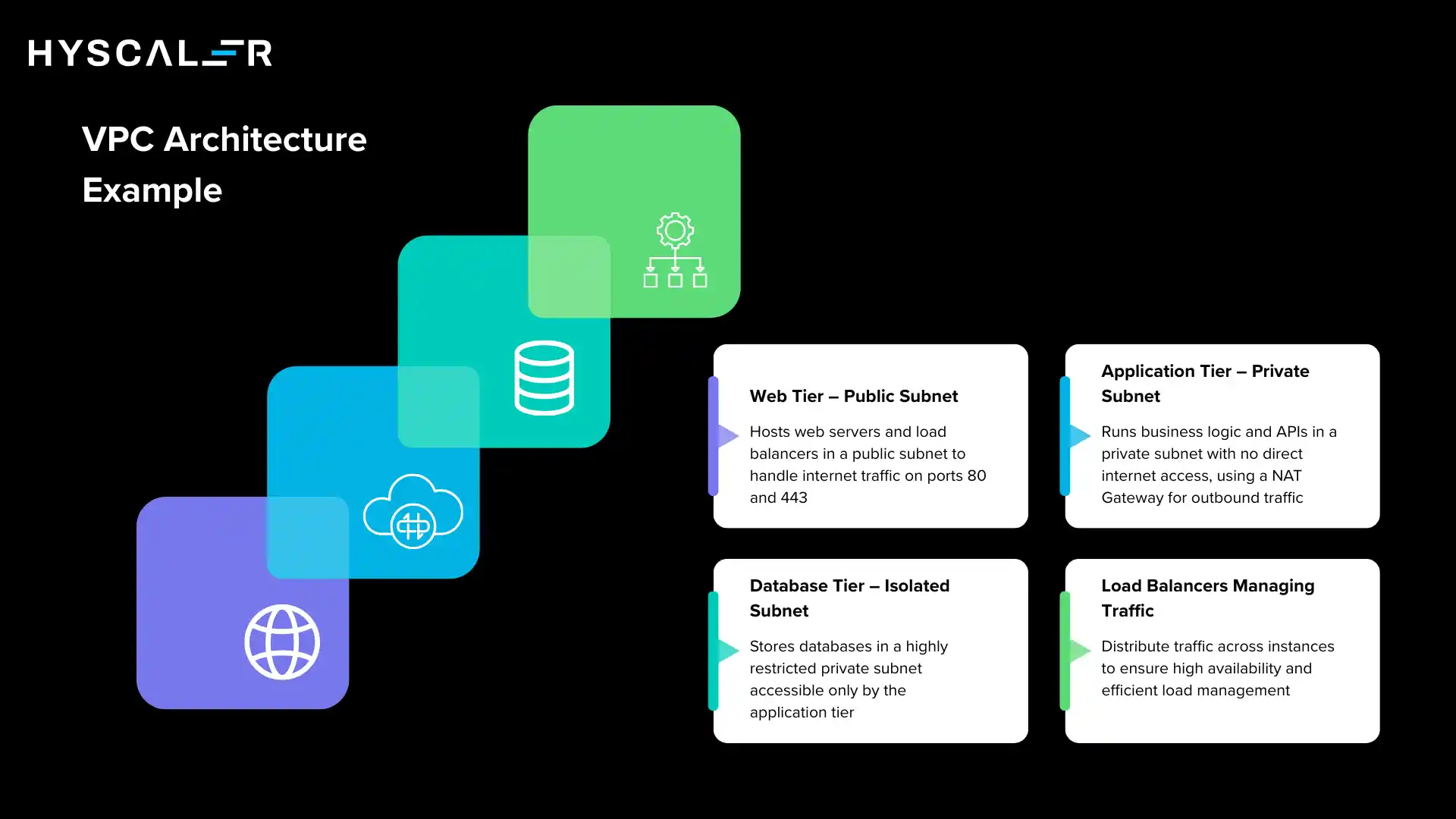
Web Tier – Public Subnet
The web tier hosts load balancers and web servers that accept internet traffic.
These resources sit in a public subnet with a route to the Internet Gateway.
Security groups restrict inbound traffic to ports 80 and 443 only.
Application Tier – Private Subnet
The application layer, containing business logic, APIs, and microservices, runs in a private subnet.
It can communicate with the web tier and the database tier, but has no direct internet access.
Outbound traffic for updates or API calls is routed through the NAT Gateway.
Database Tier – Isolated from Internet
Databases are deployed in a separate private subnet with the most restrictive access controls.
Only application-tier resources are permitted to connect to the database, and there is no route to the internet whatsoever.
This tier is the most protected layer of the entire architecture.
Load Balancers Managing Traffic
Load balancers distribute incoming user traffic across multiple web-tier instances, ensuring high availability and fault tolerance.
Internal load balancers can also distribute traffic between the application and database tiers within the Virtual Private Cloud.
Virtual Private Cloud vs Public Cloud
Understanding the distinction between a Virtual Private Cloud and a standard public cloud environment is essential for making informed architecture decisions.
| Feature | Virtual Private Cloud | Public Cloud |
|---|---|---|
| Network Isolation | High – logically separated | Shared with other tenants |
| Security Control | Advanced, fully configurable | Limited, provider-managed |
| Custom Networking | Yes – full IP, routing, subnets | Minimal customisation |
| Compliance Support | Strong – auditable controls | General-purpose |
| Enterprise Use | Standard for sensitive workloads | General workloads |
| Hybrid Connectivity | VPN / Direct Connect supported | Not typically available |
| Cost Model | Pay-as-you-go + control overhead | Pay-as-you-go, simpler billing |
Common Use Cases of Virtual Private Cloud
VPCs have become the networking standard across virtually every industry that runs workloads in the cloud.
Key use cases include:
- Hosting secure enterprise applications that require strict access controls and network segmentation.
- Financial services infrastructure, like trading platforms, payment systems, and risk engines, that must meet PCI-DSS compliance and minimise attack surface.
- Healthcare data platforms hosting electronic health records (EHR) and medical imaging systems under HIPAA compliance requirements.
- SaaS platforms that use VPC peering and multi-tenant architecture to serve customers with strict data isolation requirements.
- Hybrid cloud deployments that extend on-premise data centres into the cloud for seamless infrastructure integration.
- Development and testing environments that mirror production network topologies without exposing resources externally.
Virtual Private Cloud Security Best Practices
A Virtual Private Cloud provides the tools for strong security, but proper configuration is essential.
Following these best practices will significantly reduce your risk exposure:
- Use private subnets for databases and backend services – never place databases in a public subnet.
- Implement least-privilege security groups – allow only the specific ports and protocols required by each service, and deny everything else by default.
- Enable VPC Flow Logs to capture and monitor all traffic entering and leaving your VPC, enabling threat detection and forensic investigation.
- Use VPN or private connectivity (Direct Connect, ExpressRoute, or Interconnect) for hybrid connections rather than routing sensitive traffic over the public internet.
- Encrypt all traffic between services using TLS, and use cloud-native key management services to protect encryption keys.
- Regularly audit security group rules and NACLs to remove unused, overly permissive, or outdated rules.
- Enable multi-availability-zone (multi-AZ) deployments for critical workloads to ensure resilience against infrastructure failures.
VPC Across Major Cloud Providers
All three major cloud providers offer VPC as a core networking service, though the terminology and specific feature sets differ slightly.
AWS VPC
Amazon Web Services pioneered the VPC concept, and it remains the core networking service underpinning the entire AWS ecosystem.
Every AWS account comes with a default VPC, and custom VPCs can be built with fine-grained control over subnets, route tables, Internet Gateways, NAT Gateways, security groups, and NACLs.
AWS also offers Transit Gateway for connecting multiple VPCs and on-premise networks at scale.
Azure Virtual Network (VNet)
Microsoft Azure’s equivalent is the Virtual Network (VNet).
It offers similar logical isolation, subnet design, and routing capabilities.
Azure-specific features include Network Security Groups (NSGs), Azure Firewall, and ExpressRoute for private connectivity to on-premise infrastructure.
Azure VNet integrates natively with Azure Active Directory for identity-based access control.
Google Cloud VPC
Google Cloud’s VPC is notable for its global architecture; unlike AWS and Azure, a single Google Cloud VPC can span all regions without requiring explicit peering.
This simplifies multi-region deployments significantly.
Google Cloud VPC also offers Shared VPC for centralising networking across multiple projects within an organisation, and Cloud Interconnect for private on-premise connectivity.
Challenges of Managing VPC
While VPCs deliver significant benefits, they introduce complexity that organisations must actively manage:
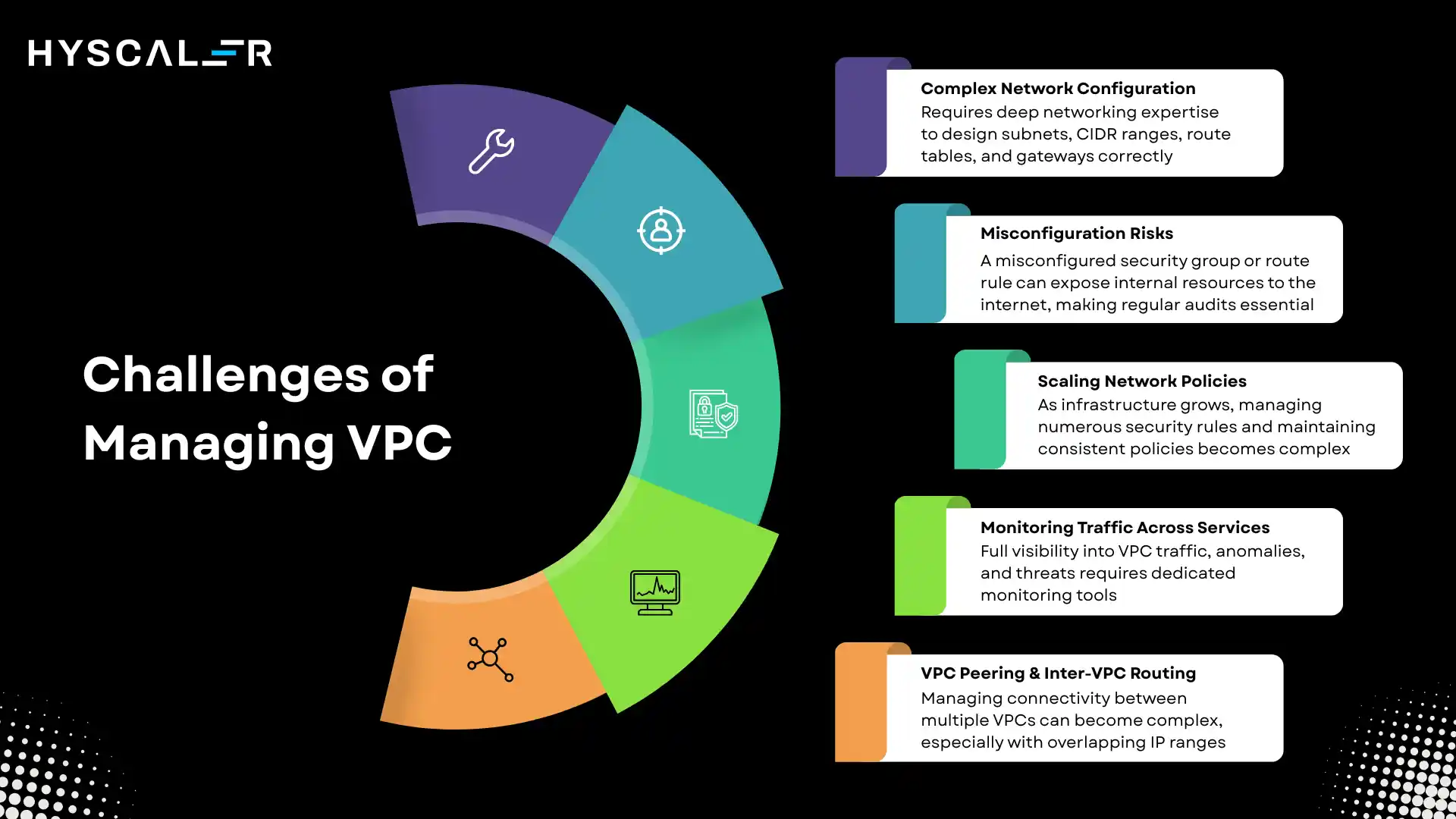
- Complex Network Configuration – designing subnets, CIDR ranges, route tables, and gateways correctly from the outset requires deep networking expertise.
- Misconfiguration Risks – a single misconfigured security group or route table rule can inadvertently expose internal resources to the internet, making regular audits essential.
- Scaling Network Policies – as infrastructure grows, managing hundreds of security group rules and maintaining consistent policies across environments becomes operationally demanding.
- Monitoring Traffic Across Services – gaining full visibility into traffic patterns, anomalies, and potential threats across a large VPC requires dedicated monitoring tools and practices.
- VPC Peering and Inter-VPC Routing – managing connectivity between multiple VPCs in a large organisation can become complex, particularly with overlapping IP ranges.
Future of Virtual Private Cloud
The evolution of cloud networking is accelerating, driven by advances in AI, security architecture, and multi-cloud strategies.
Several trends are shaping the next generation of VPC technology:
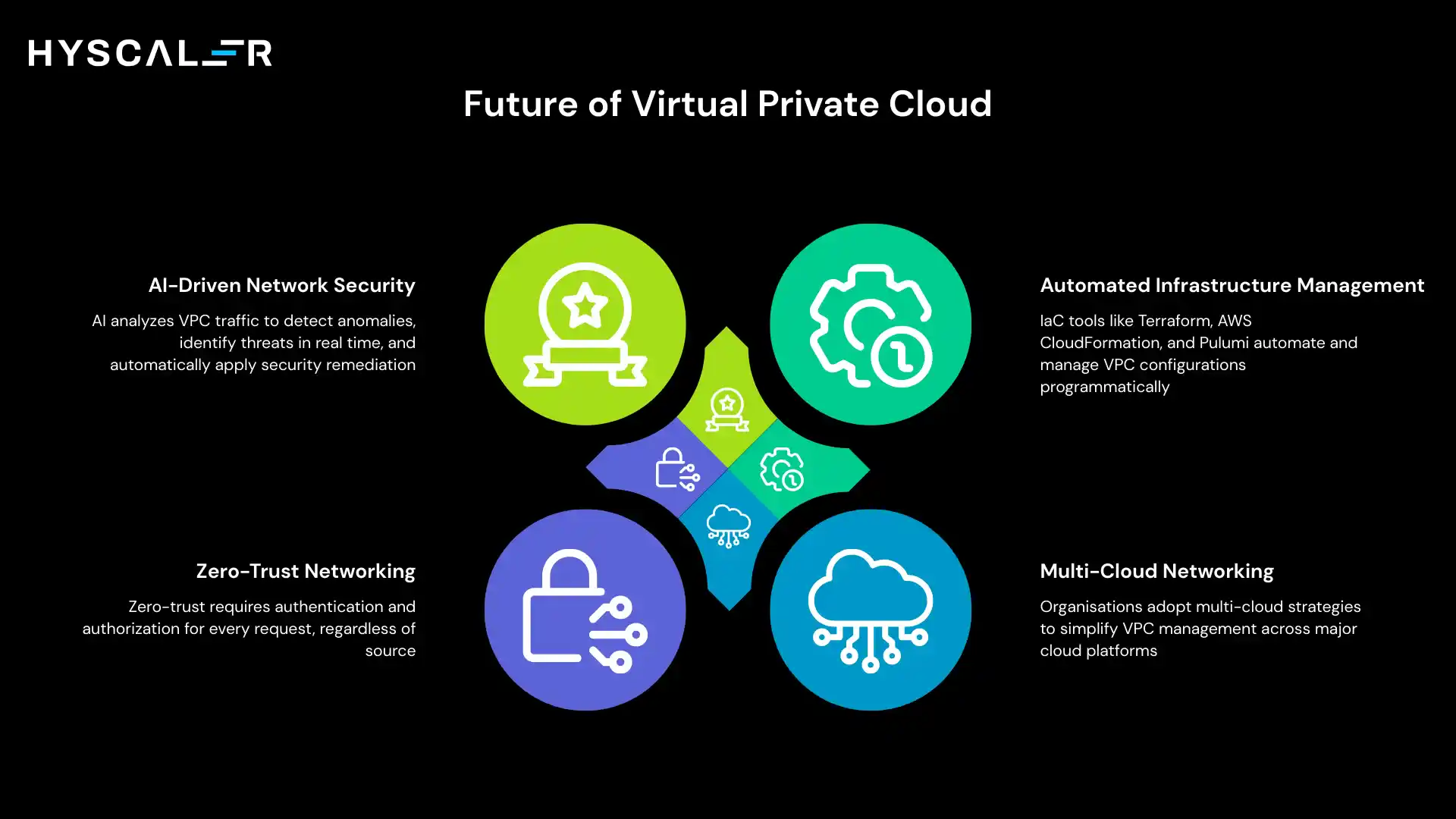
AI-Driven Network Security
Artificial intelligence is increasingly being applied to network traffic analysis within VPCs, automatically identifying anomalous patterns, detecting potential threats in real time, and suggesting or even automatically applying remediation rules.
AI-driven security promises to make VPC environments both safer and easier to manage.
Zero-Trust Networking
The traditional castle-and-moat security model, where everything inside the VPC is trusted, is being replaced by zero-trust architectures.
In a zero-trust VPC, every request is authenticated and authorised regardless of its source.
This approach is becoming the security standard for enterprises with highly distributed and dynamic workloads.
Automated Infrastructure Management
Infrastructure-as-Code (IaC) tools such as Terraform, AWS CloudFormation, and Pulumi are making it possible to define, deploy, and manage entire VPC architectures programmatically.
As AI capabilities are integrated into IaC workflows, network configuration will become increasingly automated and self-healing.
Multi-Cloud Networking
Organisations are increasingly spreading workloads across multiple cloud providers to avoid vendor lock-in and optimise for performance and cost.
Next-generation networking solutions, including cloud-agnostic overlay networks and managed multi-cloud connectivity platforms, are emerging to simplify VPC management across AWS, Azure, and Google Cloud simultaneously.
Conclusion
A Virtual Private Cloud is far more than a networking feature; it is the foundational security and infrastructure layer upon which modern enterprise cloud deployments are built.
By providing logical isolation, customisable network topology, and granular security controls, VPCs give organisations the confidence to run even their most sensitive workloads in the cloud.
Whether you are migrating legacy systems, building cloud-native applications, or architecting hybrid environments, a well-designed VPC is the essential starting point.
Understanding its components, capabilities, and best practices empowers you to build a cloud infrastructure that is not only scalable and cost-effective but also secure and compliant by design.
In 2026 and beyond, VPC remains the cornerstone of cloud architecture.
Investing in VPC design expertise is investing in the security and resilience of your entire cloud estate.
FAQ
What is the difference between a VPC and a traditional private network?
A traditional private network relies on physical hardware and dedicated infrastructure. A VPC is a software-defined private network that runs on shared public cloud infrastructure. It delivers the same logical isolation and control as a physical private network, but with the elasticity, scalability, and managed services of the cloud.
Is a VPC free to use?
Creating a VPC itself is typically free on major cloud platforms. However, associated resources such as NAT Gateways, VPN connections, Elastic IP addresses, and data transfer costs are billed separately. Always review your cloud provider’s pricing documentation for the full cost picture.
Can I connect two VPCs?
Yes. VPC Peering allows two VPCs to communicate with each other as though they were on the same network. For more complex multi-VPC topologies, services like AWS Transit Gateway or Google Cloud’s Shared VPC provide centralised connectivity management.
How many VPCs can I create?
Cloud providers impose default limits; for example, AWS allows up to 5 VPCs per region by default, but these limits can be increased by submitting a service quota increase request. Most organisations structure workloads across multiple VPCs for better isolation and management.
What are VPC Flow Logs, and why are they important?
VPC Flow Logs capture metadata about IP traffic flowing to and from network interfaces within your VPC. They are critical for security analysis, troubleshooting network connectivity issues, and meeting audit requirements for compliance frameworks such as PCI-DSS and HIPAA.
What is the difference between a Security Group and a Network ACL?
Security Groups are stateful, instance-level firewalls; responses to allowed requests are automatically permitted. Network ACLs are stateless, subnet-level firewalls that evaluate every packet independently. Both should be used together as part of a layered defence strategy.
Can a VPC span multiple regions?
In most cloud providers (AWS and Azure), a VPC or VNet is confined to a single region. Google Cloud is an exception; its VPC is a global resource that can span all regions. For multi-region deployments in AWS and Azure, separate VPCs must be created per region and connected via peering or transit services.
Is a VPC the same as a private cloud?
No. A private cloud is a dedicated physical environment managed solely for one organisation. A VPC is a logically isolated partition within a shared public cloud. While a VPC delivers similar network isolation, it still runs on the cloud provider’s shared physical infrastructure.