Table of Contents
The Application Programming Interface (API) functions as the essential connective tissue for modern digital transformation. It facilitates communication between disparate software systems. This allows organizations to share data with customers and partners seamlessly. As businesses transition toward cloud-native architectures, API security has shifted from an optional add-on to a strategic necessity. It ensures business continuity by protecting the backend frameworks that power mobile apps and SaaS platforms.
The Open Worldwide Application Security Project (OWASP) defines API security as focusing on strategies and solutions to mitigate unique vulnerabilities. These risks stem from how APIs expose internal application logic and sensitive data. Neglecting these risks leads to severe consequences. Reports indicated that unique attackers targeting these interfaces grew by 400% within a six-month period in 2023. Furthermore, approximately 94% of companies experienced production issues related to their APIs in 2022.
In 2017, Gartner predicted that these interfaces would become the primary attack vector. Recent data proves this prediction correct. Strategic leaders now view this as a C-level priority. Failure to secure these connections results in brand erosion and unplanned engineering debt.
Traditional security measures fail in this fragmented landscape. A conventional Web Application Firewall (WAF) relies on a clear network perimeter. This “castle and moat” security model inspects traffic at the entrance. However, modern applications utilize highly distributed microservices. A single external request often triggers dozens of internal, “east-west” API calls. If an organization only monitors the perimeter, these internal interactions remain unprotected. Dedicated API security requires monitoring every individual API endpoint and validating internal traffic. Understanding these foundational differences is the first step in recognizing how the threat landscape has shifted.
The Evolution of API Threats
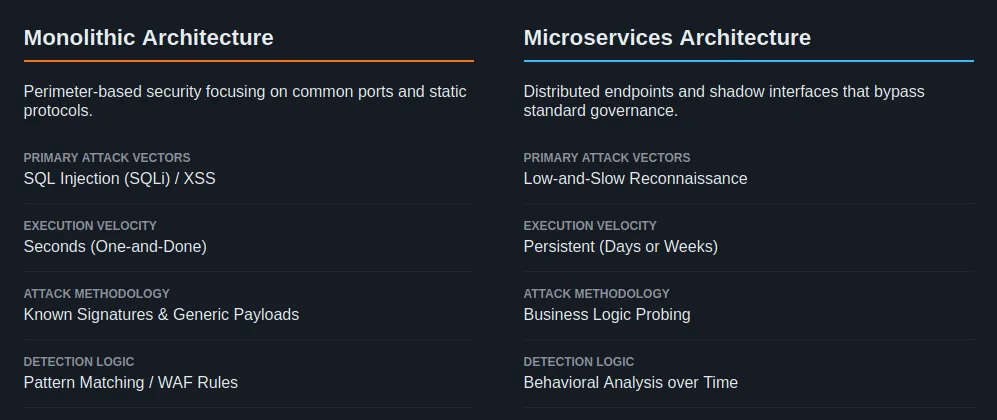
The transition from monolithic architectures to cloud-native microservices has fundamentally altered the attack surface. In the past, organizations protected a few common ports and static protocols. Today, web applications feature thousands of endpoints across various technologies. This expansion makes visibility the primary challenge for security architects. Architects must now account for shadow interfaces that bypass standard governance.
Attack methodologies have also evolved toward higher sophistication. We can contrast the “one-and-done” attacks of the past with modern threats.
- Past Attacks: Cybercriminals previously focused on high-volume exploits. These attacks, such as SQL injection or Cross-Site Scripting (XSS), occur in seconds. They typically rely on known signatures and generic payloads.
- Modern Threats: Modern attackers use “low-and-slow” techniques. These campaigns can last days or weeks. An attacker conducts extensive reconnaissance to probe the unique business logic of a specific API endpoint.
Reconnaissance plays a decisive role in modern security threats. An attacker learns how an API behaves to find unique logic flaws. They might reverse-engineer a mobile app to find a deprecated API request URL. By probing these undocumented endpoints, they find ways to exfiltrate sensitive data. Traditional tools struggle to detect these patterns because the individual calls appear legitimate. Only behavioral analysis over time identifies the malicious intent.
The GenAI Frontier and New Risks
The rise of Generative AI introduces a new layer of complexity. Modern organizations now utilize APIs to connect with Large Language Models (LLMs). These integrations often use Model Context Protocol (MCP) servers to bridge data and AI agents.
This creates a new “shadow AI” problem. Developers might integrate AI services without notifying security teams. These AI-mediated calls often handle highly sensitive information. An attacker could exploit an unmanaged AI agent to trigger unauthorized actions. This makes it mandatory to inventory every connection to GenAI models. You must treat these as critical points of failure in your architecture.
3 Types of APIs and Security Considerations
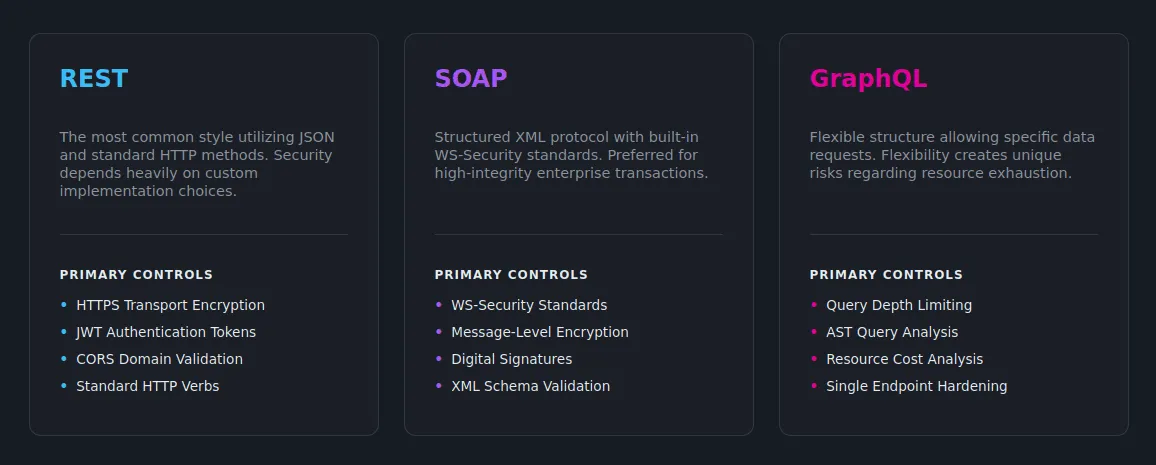
Not all APIs are created equal. The choice of protocol dictates the available security controls. It also defines the complexity of the security architecture. Architects must understand the specific requirements for the most common implementations.
1. REST API Security
A REST API (Representational State Transfer) is the most common architectural style. It utilizes JSON for data transfer and relies on standard HTTP methods. Security for a REST API depends entirely on implementation choices. Developers must enforce transport layer security (HTTPS) to encrypt data in transit. They also use tokens like JWT to authenticate users. Failure to use Cross-Origin Resource Sharing (CORS) headers can also expose these interfaces to unauthorized domains.
2. SOAP Security
The Simple Object Access Protocol (SOAP) is a structured protocol using XML. Unlike other formats, SOAP has built-in security features through the WS-Security standard. This standard provides message-level integrity and confidentiality. SOAP also utilizes digital signatures to protect data. While complex, SOAP is often preferred for enterprise transactions requiring rigorous error handling. Architects must use XML validation to prevent XML injection and related attacks.
3. GraphQL Security
GraphQL allows clients to request specific data structures from a single API endpoint. This flexibility creates significant risks. Clients can craft deeply nested queries that overwhelm the API server. This can lead to a denial-of-service (DoS) event. To mitigate this, architects must set query depth limits. You must also analyze the abstract syntax tree (AST) of incoming queries.
Comparative Analysis of API Protocols
| Feature | REST API | SOAP | GraphQL |
| Data Format | JSON | XML | JSON |
| Security Strength | Implementation-dependent | Built-in (WS-Security) | Implementation-dependent |
| Primary Vulnerability | Business logic flaws | XML Injection | Resource Exhaustion (DoS) |
| Communication | HTTP/S | HTTP, SMTP, TCP | HTTP/S |
Regardless of the protocol, systemic risks appear across all implementations. These risks require a unified approach to governance.
Common API Security Risks (The OWASP Perspective)
The API security provided by OWASP serves as a strategic roadmap. These risks represent the most frequent avenues for unauthorized API access. Understanding these API vulnerabilities is essential for engineering teams.
Broken Object Level Authorization (BOLA)
BOLA is the most significant vulnerability in modern environments. It occurs when an application fails to validate permissions for specific objects.
Critical Finding: Broken Object Level Authorization represents approximately 40% of all API calls involved in successful attacks.
An attacker exploits BOLA by manipulating an ID within an API request. For example, a user might change a numeric ID in a URL to access another customer’s data. If the server does not check ownership, the attacker gains unauthorized access. This often leads to full account takeover.
Broken User Authentication
Authentication mechanisms are often public, making them easy targets. If the process is weak, an attacker uses brute force attacks to gain entry. Common security issues include inadequate password complexity or long token rotation times. Organizations often mistakenly use API keys as the sole identity verification method. When authentication fails, an attacker acts as legitimate users to steal data.
UnRESTricted Resource Consumption
This vulnerability relates to how systems handle request volume. If an endpoint does not limit resource consumption, it becomes susceptible to DoS. High request volumes consume CPU, memory, and storage. This degrades performance and makes systems vulnerable to automated token cracking.
Broken Object Property Level Authorization
This risk combines excessive data exposure and mass assignment. It occurs when an API exposes all properties of an object. Developers then rely on the API client to filter the data. An attacker intercepts the raw response to find hidden fields. In mass assignment, they might update sensitive properties that the developer forgot to protect. Identifying these API vulnerabilities is the first step in implementing definitive countermeasures.
Core API Security Controls
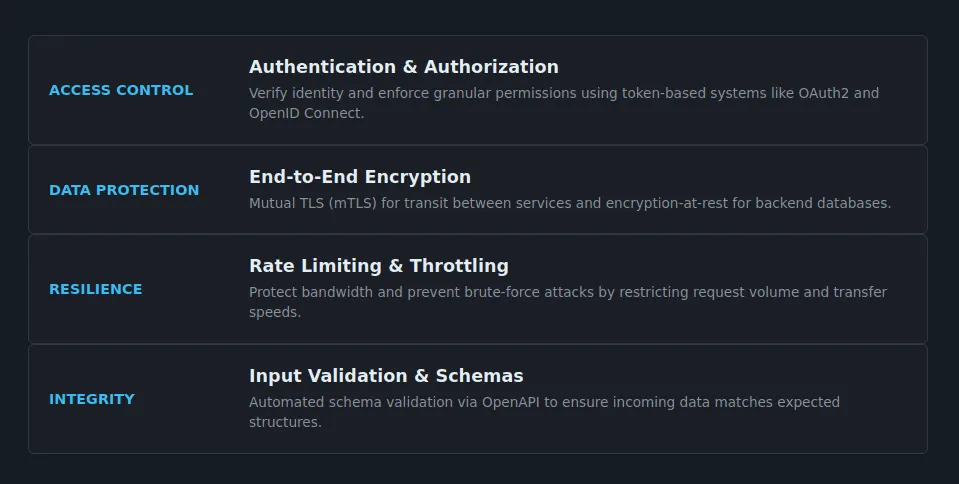
Architecting resilience requires a “defense-in-depth” strategy. Relying on a single API gateway is insufficient. A gateway provides visibility for “north-south” traffic but often ignores internal communication. Architects should combine a gateway with a Service Mesh. A Service Mesh handles the complex “east-west” interactions between microservices. This ensures every internal call receives proper scrutiny.
Authentication and Authorization
Architects must differentiate between these two concepts. To authenticate is to verify that a user is who they claim to be. In contrast, access control (authorization) verifies permissions for specific actions. Organizations should adopt token-based systems like OAuth2 or OpenID Connect. These systems allow for fine-grained permissions without exposing the actual credential.
Encryption
Encryption must protect data at every stage of the journey. Mutual TLS (mTLS) ensures that communication between microservices remains encrypted and verified. Additionally, encryption at REST protects data stored in backend databases. This ensures that even if a storage layer is compromised, the information remains unreadable.
Rate Limiting and Throttling
Rate limiting is an essential tool to prevent brute force attacks. It RESTricts the number of requests a client can make within a timeframe. Throttling controls the speed of data transfer. Together, these controls protect bandwidth. They ensure that legitimate users can access the service during a coordinated attack.
Input Validation and Schemas
The API server must validate every piece of incoming data. It should check that data matches the expected schema. This prevents injection attacks where an attacker sends malicious commands. Using a machine-readable format like OpenAPI allows for automated schema validation at the gateway level.
Real-World API Attack Examples
Historical failures illustrate the impact of common API security gaps. These incidents often stem from overlooked flaws rather than complex new exploits.
Case Study 1: E-commerce Logic Abuse
In one incident, an attacker targeted an e-commerce application. By reverse-engineering the mobile app, they discovered a deprecated URL used for product data.
- Vulnerability Trigger: The deprecated endpoint required no authentication.
- Exploitation: The attacker identified an injection flaw in the product ID field.
- Business Impact: The attacker used the flaw to execute shell commands. They installed bitcoin mining software on the API server, disrupting service for days. This represents a failure of asset management and input validation.
Case Study 2: Unauthorized Data Retrieval via ID Manipulation
A major provider experienced a breach due to a classic BOLA flaw. The API exposed object identifiers in the URL structure.
- Vulnerability Trigger: The system failed to verify if the user owned the data object.
- Exploitation: Attackers used scripts to increment IDs in their API calls.
- Business Impact: Attackers exfiltrated millions of records containing sensitive data. This incident falls under the OWASP API risk for broken object-level authorization.
These examples show that attackers target forgotten “zombie” interfaces. These incidents prove the need for robust best practices.
Strategic Recommendations and Best Practices
Securing the modern landscape requires a full API lifecycle approach. “Shifting left” by testing code early is necessary. However, many security vulnerabilities only manifest during runtime. Architects must balance development-time testing with proactive runtime protection.
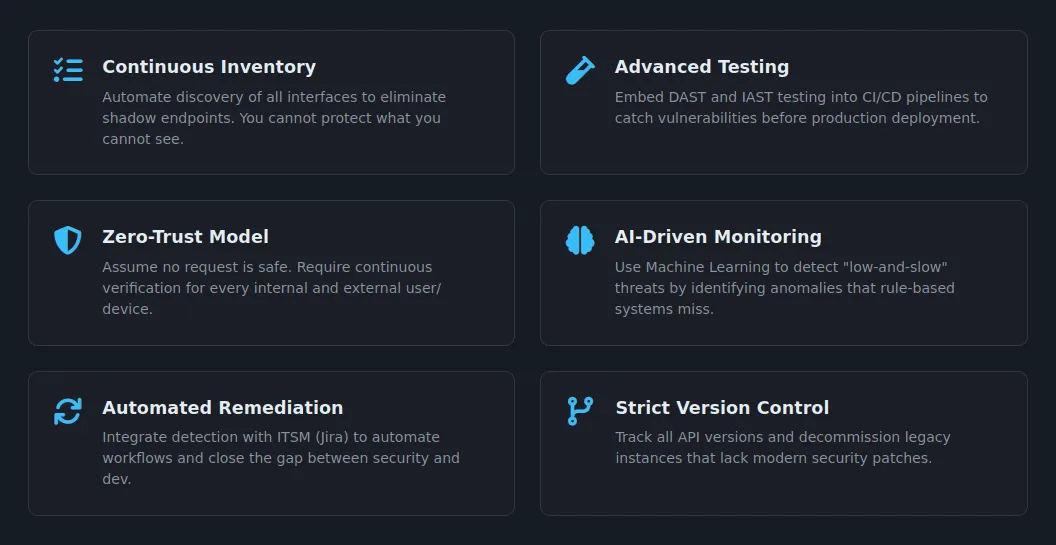
Actionable Best Practices
- Maintain a Continuous Inventory: Use security tools that automatically discover all interfaces. This eliminates shadow endpoints deployed without oversight. You cannot protect what you cannot see.
- Integrate Advanced Security Testing: Implement security testing early in the CI/CD pipeline. Use Dynamic Application Security Testing (DAST) and Interactive Application Security Testing (IAST). These tools should trigger automatically during Pull Requests (PRs). This ensures you catch vulnerabilities before they reach production.
- Adopt a Zero-Trust Security Model: Assume that no API request is safe. This security model requires continuous verification of every user and device. It ensures that internal traffic is as secure as external traffic.
- Deploy AI-Driven Monitoring: Utilize security solutions that offer machine learning for behavior analysis. These tools detect “low-and-slow” threats by correlating millions of attributes. They identify anomalies that rule-based systems miss.
- Automate Remediation Workflows: Integrate your detection tools with ITSM platforms like Jira. Create automated workflows to verify fixes and close the loop between security and development.
- Manage API Versions Strictly: Track different API versions and decommission old ones. Attackers target legacy versions that lack modern security patches.
The API server must act as a final gatekeeper. Sanitizing all input remains the primary defense against command-based attacks. By treating this as an ongoing process, organizations build true resilience.
Key Takeaways
This guide provides a framework for securing backend services in an evolving landscape. Effective protection requires a shift from static perimeters to contextual, behavioral defense.
- Visibility is the Foundation: Automated discovery must eliminate shadow APIs and catalog AI-mediated connections.
- Logic Over Signatures: Traditional rules cannot stop business logic attacks. You need behavior-based runtime protection.
- Authorization is the Top Priority: BOLA remains the most frequent vulnerability. Implement rigorous access control at the object level.
- Integrate the Full Lifecycle: Security must exist in development, staging, and production. Use automated DAST to catch security vulnerabilities early.
- Contextual AI Defense: Protect against “low-and-slow” threats by analyzing the context of calls over time.
In an interconnected world, API security is an ongoing process of discovery and monitoring. Implementing these strategies ensures your digital pathways remain secure for innovation.
FAQs
What is API security?
API security defends application programming interfaces against malicious attacks, preventing data theft and service crashes. Effective strategies ensure only authorized users access private information. Unprotected APIs are the leading cause of data breaches.
What are the types of API security?
Organizations secure APIs based on their specific architectural patterns.
1. REST Security: Focuses on standard web methods (GET, POST). Uses HTTPS and tokens for verification. Security must be integrated into the API design.
2. SOAP Security: Uses a structured XML protocol. Employs built-in standards like WS-Security and digital signatures for enterprise-level protection.
3. GraphQL Security: Manages a single endpoint. Uses query depth limits and request throttling to prevent complex queries from overwhelming the server.
How often should I audit my APIs?
Continuously audit APIs. Security teams demand real-time updates since developers frequently change code. Continuous discovery immediately identifies new or altered endpoints.
How does rate limiting enhance API security?
Rate limiting restricts client request volume. This blockade stops brute-force attacks and prevents service outages. It defends the server against traffic spikes.
How can I ensure that deprecated API versions don’t pose security risks?
Strictly inventory all active API versions. Attackers exploit forgotten, old endpoints to bypass security. Compare documentation against current traffic. Find and immediately delete risky, outdated versions.
How can I monitor and log API activity effectively?
Log every API call. This builds a baseline of normal behavior. Use telemetry data to instantly spot unusual spikes or suspicious patterns. Detailed logs provide vital evidence to analyze and resolve breaches.
How do I integrate identity with data while preserving privacy?
Mask sensitive details in your logs to protect user privacy. Use external identity stores and encrypted tokens like OAuth to verify users safely. This keeps personal data hidden even while the system confirms identity.