Table of Contents
Ransomware has evolved from a simple “pay to unlock your files” scheme into a multi-layered cyber siege that hits businesses from three directions at once. Effective ransomware prevention in 2026 demands a proactive, intelligent, and layered cybersecurity strategy, one that accounts for AI-powered malware attacks, criminal insider recruitment, and simultaneous DDoS attacks designed to break your defences fast. Without a clear ransomware prevention plan in place, no organization is truly safe from the growing ransomware threat.
Here is everything your business needs to know to stay protected.
What Is Triple Extortion Ransomware, and How Does It Work?
How Ransomware Evolved Over Time
Early ransomware was blunt: encrypt files, demand payment, and hope the victim pays.
Then double extortion emerged; attackers began staging data theft before triggering file encryption, threatening to publish stolen data publicly.
Without a ransomware prevention strategy, both scenarios leave your business exposed to devastating cyber extortion.
How Ransomware Gangs Use DDoS Attacks as Extortion Weapons
Triple extortion adds a third weapon: DDoS attacks.
If victims refuse to pay, attackers flood public-facing systems with junk traffic, knocking websites and portals offline. Running file encryption and DDoS attacks simultaneously is designed to exhaust victims into paying fast.
This combination of data theft, file encryption, and DDoS attacks makes cyber extortion uniquely destructive in 2026.
Step-by-Step: What Happens During a Triple Extortion Attack
- Stage 1: Reconnaissance: Attackers silently map your network for weeks, identifying high-value data and weak credentials without triggering alerts.
- Stage 2: Data Theft: Files are quietly exfiltrated before any ransom demand appears, invisible without advanced threat intelligence monitoring in place.
- Stage 3: File Encryption: Systems are locked, operations halt, and the ransom note arrives. Without ransomware prevention controls active, there is no way to stop it mid-attack.
- Stage 4: DDoS Amplification: If negotiations stall, DDoS attacks launch against public infrastructure, completing the cyber extortion cycle.

The Rise of Ransomware-as-a-Service: Why Anyone Can Launch an Attack in 2026
How RaaS Lowered the Barrier for Cybercriminals
Ransomware-as-a-Service (RaaS) has democratized cybercrime.
RaaS operators provide ready-made malware tools, infrastructure, payment portals, and technical support to affiliates who carry out attacks and split the profits; no advanced skills are required. This malware-for-hire model makes ransomware prevention significantly harder. Attacks surged 47% in 2025, with over 7,200 publicly reported incidents. Malware prevention at scale is now a critical cybersecurity priority as the ransomware threat becomes truly global.
Insider Threat: How Ransomware Groups Are Recruiting Your Employees
One of the most alarming trends in 2026 is the active recruitment of corporate insiders by ransomware gangs. Groups like Medusa employ dedicated “reach-out managers” who approach employees with financial incentives in exchange for access credentials. In December 2025, two cybersecurity professionals pleaded guilty to collaborating with the BlackCat/ALPHV group. Ransomware prevention now extends beyond firewalls into human risk management. Data theft through insider access remains one of the hardest threats to detect without dedicated threat intelligence.
Industries and Sectors Being Targeted Most in 2026
No industry is immune to the ransomware threat. Manufacturing leads attack frequency, with 62% of firms having paid ransoms. Healthcare faces average data breach costs of $10.1 million. Financial services pay a median ransom of $2 million per incident, stark evidence of an escalating ransomware threat across every sector.
How AI-Powered Ransomware Attacks Are Changing the Threat Landscape
AI-Driven Phishing: Deepfakes and Hyper-Personalised Lures
Generative AI allows attackers to craft hyper-personalised phishing emails that convincingly impersonate colleagues and executives. Deepfake audio is being used in social engineering calls impersonating IT support or finance staff. Effective malware prevention must account for these AI-driven vectors, which no cybersecurity tool alone can stop without strong ransomware prevention behind it.
Self-Mutating Malware: How AI Helps Ransomware Evade Traditional Defences
AI-generated malware can mutate its own code signatures in real time, making each variant unique and rendering signature-based malware prevention tools far less effective. Modern malware prevention requires behavioural analysis and machine learning, not legacy signatures. Automated AI reconnaissance also scans thousands of organizations simultaneously, identifying vulnerabilities in minutes. Threat intelligence platforms that surface these scans early give defenders the critical warning they need before damage occurs.
The Real Cost of a Triple Extortion Ransomware Attack on Your Business
Financial Damage
The average total cost of a ransomware data breach now stands at $5.08 million, with the ransom representing only about 15% of that figure. Downtime, IT recovery, legal fees, and crisis communications make up the rest. Average downtime spans 24 days, and 69% of businesses that paid were attacked again, making payment a failed ransomware prevention strategy.
Regulatory Consequences: GDPR, HIPAA, and Data Breach Fines
A data breach does not end when systems come back online. Under GDPR, data breach incidents must be reported within 72 hours; HIPAA mandates notification within 60 days. Inadequate cybersecurity and malware-prevention measures can result in fines exceeding the ransom amount. Proactive ransomware prevention reduces both the likelihood of a data breach and the regulatory consequences that follow.
Reputational and Long-Term Business Damage
Around 60% of businesses reported revenue loss, and 53% reported lasting brand damage after an attack. Where data theft led to publicly leaked customer data, the reputational fallout can be permanent, compounding financial losses well beyond the initial incident.
Ransomware Prevention Strategies Every Business Must Have in 2026
Zero Trust Architecture: Never Trust, Always Verify
Zero Trust ransomware prevention operates on one principle: no user, device, or system is automatically trusted. It counters lateral movement directly if one endpoint is compromised; micro-segmentation stops free network movement. MFA, least-privilege access, and behavioural monitoring are core controls. When a data breach does occur, Zero Trust contains the blast radius, making it one of the highest-impact ransomware prevention investments available.
Advanced Threat Intelligence for Early Ransomware Detection
Threat intelligence gives your security team real-time visibility into active campaigns and indicators of compromise, which is especially critical for detecting quiet data theft before file encryption begins. Integrating threat intelligence into DDoS attacks and ransomware threat monitoring is one of the highest-value ransomware prevention investments your organization can make today.
DDoS Protection: How to Stay Online During an Active Extortion Campaign
DDoS protection is now a non-negotiable defence layer. Cloud-based DDoS protection absorbs malicious traffic in real time, keeping you operational during active DDoS attacks. Without DDoS protection, even businesses with strong cyber defences can be overwhelmed during a live cyber extortion campaign. DDoS protection must cover APIs and customer portals, not just your public website.
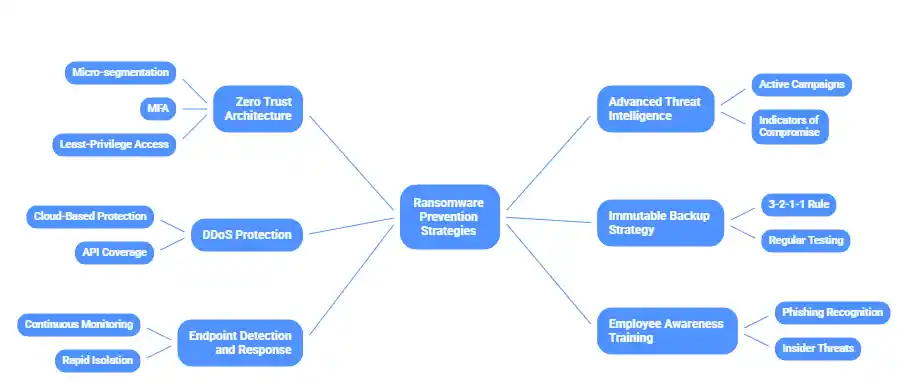
Immutable Backup Strategy
Immutable, air-gapped backups are your safety net against file encryption, but only if properly isolated. Follow the 3-2-1-1 rule: three copies, two media types, one offsite, and one completely offline. Test them regularly; an untested backup is a false sense of security. A robust backup strategy is fundamental to defending against ransomware and ensuring long-term cybersecurity resilience.
Endpoint Detection and Response (EDR)
EDR goes beyond antivirus by monitoring endpoint behaviour continuously and enabling rapid device isolation before malware spreads. Modern platforms use machine learning to catch self-mutating malware that signatures miss. Without dedicated malware prevention tooling, the ransomware threat will always find a foothold. Pair with 24/7 MDR for maximum malware prevention coverage.
Employee Awareness Training
With AI crafting near-perfect phishing lures and ransomware gangs recruiting insiders, employee training must be an ongoing programme, not an annual checkbox. Train staff to recognize phishing and understand they may be directly approached with incentives for data theft. This human layer of cybersecurity is essential to cyber extortion defence and comprehensive ransomware prevention.
Ransomware Readiness Checklist
10 Questions to Audit Your Ransomware Prevention Posture
| # | Audit Question | Area |
| 1 | Is MFA enforced across all systems and remote access points? | Access Control |
| 2 | Do you have 24/7 EDR or MDR monitoring in place? | Malware Prevention |
| 3 | Are your backups immutable, air-gapped, and regularly tested? | File Encryption Defence |
| 4 | Is cloud-based DDoS protection covering all public-facing infrastructure? | DDoS Protection |
| 5 | Does threat intelligence feed into your SOC in real time? | Threat Intelligence |
| 6 | Have employees completed a phishing simulation in the last 90 days? | Human Risk |
| 7 | Does your incident response plan cover triple extortion and cyber extortion scenarios? | Incident Response |
| 8 | Is micro-segmentation preventing lateral movement across your network? | Network Security |
| 9 | Is software patching on a defined, regular schedule? | Vulnerability Management |
| 10 | Is your cybersecurity insurance policy current and ransomware-specific? | Cyber Insurance |
Conclusion
Triple extortion ransomware combines file encryption, data theft, and DDoS attacks into a coordinated cyber extortion campaign designed to leave businesses with nowhere to turn. Add AI-powered malware and criminal insider recruitment, and the ransomware threat in 2026 is unlike anything most organizations have prepared for.
The average data breach now costs $5.08 million, attacks surged 47% in 2025, and 69% of those who paid were attacked again. Ransomware prevention cannot be an afterthought. Waiting before investing in malware prevention, threat intelligence, and DDoS protection against the ransomware threat is not a strategy; it is the most expensive mistake your business can make.
Start your ransomware prevention audit today. The ransomware threat is not slowing down, but with the right ransomware prevention strategy and a strong cybersecurity foundation, your business can be ready to face it head-on.
FAQs
What is triple extortion ransomware?
Triple extortion ransomware is a cyberattack where attackers steal data, encrypt files, and launch DDoS attacks simultaneously to pressure victims into paying quickly.
How is triple extortion ransomware different from double extortion?
Double extortion involves data theft and encryption, while triple extortion adds DDoS attacks, increasing disruption and forcing faster ransom decisions.
How do ransomware attackers gain initial access to a network?
Attackers gain access through phishing emails, stolen credentials, unpatched vulnerabilities, and exposed remote access systems like RDP.
What is ransomware-as-a-service (RaaS) and how does it work?
RaaS is a model where developers provide ransomware tools to affiliates, who launch attacks and share a portion of the ransom profits.
What are the early warning signs of a ransomware attack?
Signs include unusual login activity, slow systems, unexpected file changes, and suspicious network traffic.
How do AI-powered ransomware attacks bypass traditional security tools?
AI-powered ransomware evades detection by changing its code, mimicking user behaviour, and using highly targeted phishing techniques.
What is the best ransomware prevention strategy for 2026?
A layered approach using Zero Trust, EDR, backups, threat intelligence, and employee training offers the strongest protection.
How does DDoS protection help during ransomware attacks?
DDoS protection keeps systems online by absorbing malicious traffic, preventing attackers from disrupting operations and adding pressure during ransomware extortion attempts.
Does cyber insurance cover ransomware attacks?
Many cyber insurance policies cover ransomware attacks, including recovery costs and downtime, but coverage depends on policy terms and requires strong security practices in place.