Table of Contents
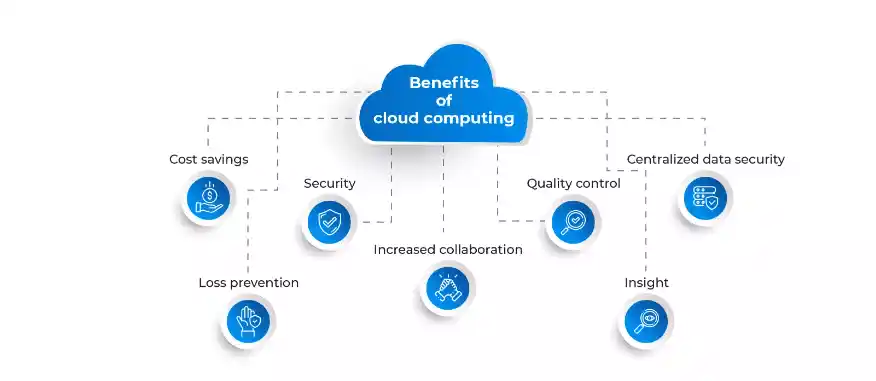
In the year 2016 State of the Cloud Survey, a staggering 95% of respondents were utilizing cloud technology, highlighting its burgeoning dominance. However, the inherent nature of cloud computing brings the potential for significant security breaches, posing a substantial risk to organizations. Data security emerges as a paramount concern among IT professionals in the realm of Cloud Application Development.
What is Cloud Application Development?
The surge in demand for cloud-based applications has sparked a corresponding rise in the development of these applications, leading to significant growth and consolidation within the cloud-computing market over recent years.
Cloud applications and services, whether we’re aware of it or not, have become ubiquitous in our daily lives. This is true for businesses as well, which have increasingly turned to cloud-based applications and services to power their operations, often without fully realizing it. For instance, if your business utilizes Software as a Service (SaaS) tools, then you’re already engaging with cloud applications. Yet, cloud applications extend far beyond just SaaS solutions.

So, how can IT managers fortify their defenses while still fostering innovation, accessibility, and flexibility in cloud application development? This article delves into seven strategic tips to bolster cloud security within organizations.
Strengthening Cloud Security 7 Tips to Protect
1. Empower Through Education
A critical step in enhancing security within Cloud Application Development involves empowering the entire organization through education. By instilling robust defense practices, companies can significantly reduce their susceptibility to security breaches. This involves several key actions:
- Cultivating a Culture of Security: Engaging every member of the organization in security protocols helps foster a culture of accountability and ownership over security responsibilities.
- Actionable Response Plans: Developing a comprehensive action plan provides employees with a clear guide for addressing security concerns, ensuring everyone knows how to respond to various scenarios.
- Practical Security Drills: Conducting spontaneous security drills, such as simulated phishing attacks, reinforces the retention of security knowledge and prepares employees for the real world.
2. Formulating a Robust Data Backup Strategy
As cloud technology continues to evolve, the risk of data loss becomes a prominent concern. Establishing a secure data backup system is essential for ensuring both data and business continuity. This includes:
- A security framework that enforces consistent data protection policies across various cloud services can significantly reduce the complexity of key management.
3. Enforcing Rigorous Access Control
- In Cloud Application Development, managing who has access to what data is crucial. Stringent access controls help mitigate risks by integrating user identities with backend directories.
- Even for external parties, this careful management of access privileges ensures that sensitive data remains protected.
4. Prioritizing Encryption in Cloud Application Development
- Encryption stands as the bedrock of security within cloud application development. By encrypting data before it leaves the organizational infrastructure, businesses can significantly bolster their defenses against unauthorized access.
- Control over encryption keys is critical; it ensures that data access requires explicit authorization from the data owner, thus enhancing security, particularly in environments managed by third-party providers.
- This level of control is indispensable for maintaining the confidentiality and integrity of data as it traverses the expansive and nebulous terrain of the cloud.
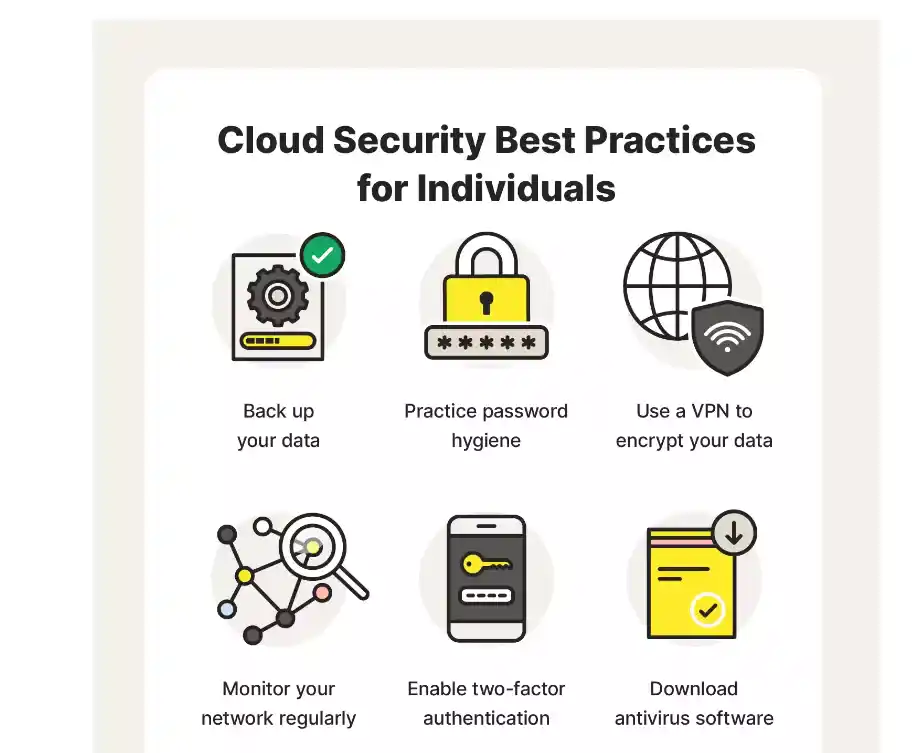
5. Strengthening Password Policies to Secure Cloud Applications
- The vulnerability of passwords is a well-documented concern in cybersecurity circles. Many passwords, despite appearing complex, can be swiftly compromised using sophisticated techniques.
- In the context of cloud application development, implementing robust password protocols is not just advisable; it’s essential.
- By utilizing an open source password manager and mandating passwords that incorporate a mix of characters, numbers, and symbols, and enforcing regular updates, organizations can create a more formidable barrier against cyber-attacks.
- This approach not only deters hackers but also plays a pivotal role in securing cloud applications from potential breaches.
6. Comprehensive Testing: A Hacker’s Perspective on Cloud Security
- Adopting a hacker’s mindset for security testing is a proactive strategy in cloud application development.
- Comprehensive testing, including penetration testing, is invaluable for uncovering vulnerabilities that could potentially be exploited by malicious actors.
- Such testing simulates real-world attacks, providing insights into the resilience of cloud applications and the effectiveness of existing security measures.
- Identifying and addressing these vulnerabilities promptly ensures that cloud applications remain secure against both internal and external threats, thereby preserving the integrity and reliability of cloud-based solutions.
7. Implementing Exhaustive Cloud Governance for Compliance and Data Privacy
- The establishment of comprehensive cloud governance is critical for ensuring that cloud application development aligns with legal compliance and data privacy standards.
- This governance framework should encapsulate continuous training for staff, strict enforcement of usage policies, regular risk assessments, and a nimble approach to the evolving security and regulatory landscape.
- By categorizing data based on sensitivity and applying tailored security measures, organizations can safeguard against breaches and unauthorized access.
- Moreover, exhaustive cloud governance fosters a culture of security consciousness and accountability, which is instrumental in mitigating risks and enhancing the overall security posture of cloud applications.
What are three essential security measures implemented to safeguard cloud environments?
In the realm of Cloud Application Development, safeguarding data and applications within the cloud is paramount. Here are three pivotal security measures integral to protecting cloud environments:
- Robust Access Control Systems: Implementing stringent access control mechanisms is foundational for securing cloud-based applications. These systems ensure that only authorized users can access specific data and applications, thereby preventing unauthorized access and potential breaches.
- Comprehensive Identity Management: Identity management plays a critical role in Cloud Application Development security by managing user identities and their permissions. It involves identifying, authenticating, and authorizing individuals or groups of people to have access to applications, systems, or networks by associating user rights and restrictions with established identities.
- Advanced Authentication Protocols: Authentication mechanisms are vital for verifying the identities of users attempting to access cloud services. Techniques such as multi-factor authentication (MFA), which requires two or more verification factors, add a layer of security.
Conclusion
The safeguarding of cloud applications stands as a cornerstone of Cloud Application Development. Through the adoption of seven key strategies—from educational empowerment and robust data protection to stringent access controls and beyond—organizations can elevate their defenses against cyber threats.
This commitment not only mitigates risks but also enhances the resilience and reliability of cloud applications, underscoring the critical role of continuous security enhancement in fostering innovation and securing digital assets in the ever-evolving digital landscape.